It’s always exciting when you can expand your business’ influence with a new location, but this excitement brings with it all kinds of complications. There’s always something, whether it’s the technology for the new location or the logistics surrounding the opening. Let’s look at how you can make sure that technology is not the thing that holds your business back from opening a new location.
Jackson Thornton Technologies News + Updates
Scams are everywhere in our highly digitized world, which makes it especially important that everyone is prepared to deal with them—both personally and professionally. The publication Consumer Reports’ cover feature for its August 2023 edition is dedicated to exactly this goal: helping its readers avoid the various scams and threats out there. Let’s look at some of the advice shared in the article, and compare it to the best practices we recommend.
With collaboration remaining an important component of any successful business, it’s important to foster productivity and innovation through strategic implementation of technology solutions designed for this express purpose. Today, we want to discuss some of the aspects of collaboration you need to know to do it more effectively, as well as technology that facilitates this process.
Information technology is a constantly changing industry, with practices shifting all the time. As a result, anyone you have working on your company’s IT should be actively seeking out various certifications to confirm that they are keeping up on modern trends and standards. To help you accomplish this, we’ve put together a brief list of valuable IT certifications that your IT personnel—whether they’re in-house employees or outsourced professionals—should have.
Businesses cannot afford to grow complacent with their network security, as it could make a significant difference between falling prey to an attack and remaining secure. The process of securing a network must be looked at holistically, from top to bottom. This idea of enterprise security is not new, but even a small business needs to keep it in mind, and these solutions are more accessible than you might think.
We’ve been spending the past few weeks examining productivity and how to optimize it, and today, we felt it was necessary to address the issues that could throw the proverbial wrench into the works.
Don’t worry, though, we’re also going to touch on how you can avoid and/or mitigate the issues that might threaten your productivity.
Productivity has been, is now, and likely will forever be heralded as one of the preeminent goals for any business. As such, it makes sense to understand as much as we can about it. To do so, we’ll be examining a different aspect of productivity for the next few weeks.
First up: what is productivity, in the first place?
Back in 1995, the Association of Records Managers and Administrators were in the midst of campaigning for the renewal of the Paperwork Reduction Act. As a part of their efforts, they created National Records and Information Management Day. Over the years since, it has expanded into a week, and then into an entire month, for businesses around the world to consider their record-keeping practices.
Did you know that World Backup Day is in just a few short weeks? While it is an important occasion for businesses to recognize, data backup should really be something you think about all the time. This is because your backup is an integral part of the backup and disaster recovery portion of your overall business continuity.
While many small businesses shrug off cybersecurity needs as too expensive an investment for an organization of their size, this is a potentially catastrophic mistake. The fact of the matter is that small businesses are regularly targeted by cyberattacks, making the aforementioned cybersecurity needs even more needed.
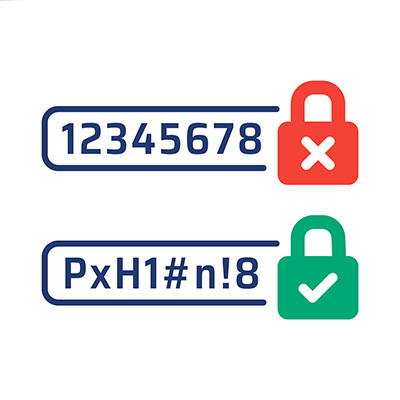
Simple passwords are often the bane of a business’ existence. If you routinely use strings like Password, 123456, Guest, or Qwerty to secure an account, then you need to reexamine your password practices before they lead to a data breach. A good password can go a long way toward helping you in this effort.
Remote work on a widespread scale was introduced in less-than-optimal circumstances, but that doesn’t mean that today’s businesses shouldn’t use it to their full advantage. Let’s discuss the situation at hand, more specifically, a few ways you and your organization can support your team as they work remotely.
How many of your employees do you think hold a second job? This isn’t a particularly outlandish concept, but one thing that has come about as a result of the COVID-19 pandemic and its surge of remote work is that some employees hold two jobs at the same time, and not in the way that you might expect.
No matter how well you protect your network, chances are you’ll suffer from some vulnerability or another. That said, you can take considerable measures toward protecting your business so you don’t have to worry so much about them. Let’s discuss how your efforts today can protect your business now and in the future.