Jackson Thornton Technologies News + Updates
We’re sure your business has at least a couple of employees who spend part of their workday in a different location, but are you doing all you can to help them be as productive as possible? While remote work is beneficial in so many circumstances, there are a lot of caveats to it that must be considered. Today, we want to go over how you can mitigate risk and keep remote work from becoming a liability for your company.
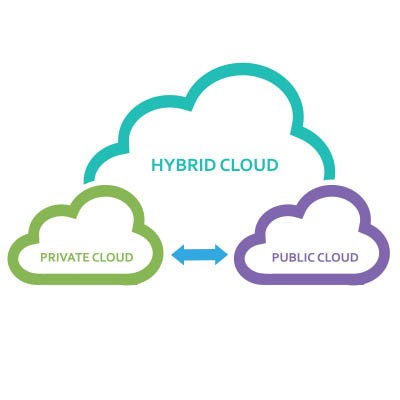
Whether you’re aware of it or not, you’re likely already utilizing the cloud in at least some capacity. The trick is to find the best way to manage your business’ cloud so that it works for your organization’s specific needs. Today, we want to look at the different types of cloud management policies and why you need to weigh your options to get the most value for your business.
It’s no secret that Google Chrome is one of the most popular web browsers in the world, if not the most popular. Still, most people don’t use the browser to its full potential, and they leave so many wasted opportunities to save time and resources on the table. Today, we want to highlight some of these tips, but also a couple of features that perhaps you didn’t know existed for Google Chrome so you can continue to get more value out of it as a business and productivity tool.
The Android operating system periodically receives updates and patches detailed in online publications called Android Security Bulletins. In the March 2025 edition, Google announced that 43 malicious bugs had been resolved, two of which were zero-day vulnerabilities.
Let’s talk about how to implement these fixes and why this is a practice that should reach every aspect of your business’ IT.
It should come as no surprise that cybersecurity is a big challenge for businesses and individuals alike. The problem: life pretty much revolves around being online these days, so there’s no avoiding it. Therefore, it’s your responsibility to ensure that any data you collect from your customers, employees, and other key stakeholders in your business is well-protected, otherwise you will face severe consequences.
Smart speakers have been around for a while, but let’s be honest—they haven’t exactly changed the world. Sure, they’re great for playing music, setting timers, and answering random trivia questions, but beyond that? Not much has evolved. So, how did we get here, and what’s next? More importantly, can they actually be useful for businesses, or are they just another gadget collecting dust?
Besides all of those people who are advocating for the scaling back or non-implementation of tools to save jobs, most people understand the benefit of automation when it makes sense. Not only do machines tend to do certain tasks more effectively, they never willingly take a day off. Unfortunately, for every task that needs to be completed less than half can be automated, and that number drops even further when you take into account everything a human does at their job. Today, there are very few jobs that can be fully automated; even as AI has begun to be used more for business. This week, we wanted to discuss why automation may not be the answer you are looking for and why training humans holds a lot of value.
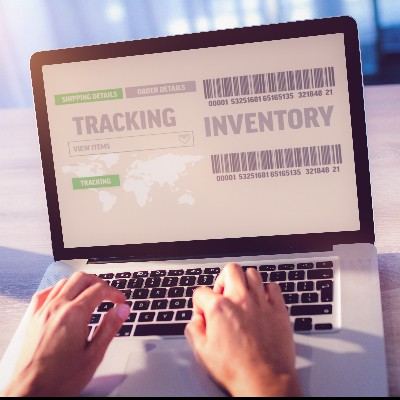
If I were to ask you what technology your business possessed and where it all was right now, could you give me an answer? If not, you’ve demonstrated the importance of keeping an accurate inventory of your business’ IT.
So, let’s go over some best practices to make managing your business’ IT inventory more effective.
We’ve all had to confirm we’re not a computer when attempting to log into an account. This is the core purpose of what once was called CAPTCHA… the Completely Automated Public Turing test to tell Computers and Humans Apart. However, it seems surprising that computers don’t easily overcome these simple-seeming tests.
Let’s dig into why these simple tests actually are effective at differentiating between human users and automated bots.
In the United States, tax season is prime time for hackers to take advantage of law-abiding, tax-paying citizens. They do this through all kinds of nefarious activities, such as phishing attacks conducted through text messages and emails claiming to be from the Internal Revenue Service. If you want to avoid getting scammed this tax season, be sure to keep the following tips in mind to stay safe while you conduct your typical tax routines.
Despite some of the headlines that we saw last year, it wasn’t all bad news regarding ransomware. Critically, 2024 saw ransomware payments plummet by hundreds of millions of dollars… despite many large-scale attacks and one record-breaking whaling payment of $75 million by one victim.
This is undeniably great to hear… but with that in mind, we cannot let ourselves slip into complacency.
Hardware is far from the most fun topic for a business owner to learn more about, but that doesn’t diminish its importance. If you want to ensure your business stays ahead of the game, then you need to be strategic about your hardware implementation. Otherwise, you risk falling behind, put your business in danger, and—even worse—imperil your budget. Today, we want to help you get the most out of your hardware, long before you have to invest in anything new.
Windows 10 is rapidly reaching the end of its secure lifetime, with support scheduled to end on October 14, 2025. While this doesn’t mean that the OS will no longer be available to use, it does mean that it will no longer be able to be safely and securely used—a critically important distinction.
That is, however, unless you pay for the Windows 10 Extended Security Updates… but is this a feasible or maintainable strategy for businesses?
Running a business is already confusing enough without worrying about security at all times. Whether you’re a small business owner or a multi-level enterprise, security is just as important for all the same reasons. Today, we want to share a couple of security strategies you can implement today to feel better about the current state of your infrastructure moving forward.
Happy Valentine’s Day! Today is a day to celebrate love, romance, and every butterfly that has ever fluttered in a stomach. However, the greatest loves can bring the greatest sorrow… particularly when the time comes to say goodbye.
Take Windows 10, for instance. PC users have loved the OS for a decade, but in a few short months, it will no longer be a good relationship for anyone—particularly business users—to maintain.
Nowadays, the average business leans pretty heavily on mobile devices to some degree, particularly as they make business productivity—and thereby, competitiveness—more easily attainable. However, this also makes it essential that a business using mobile devices has a means of managing them effectively.
Let’s explore the concept of mobile device management, and discuss some ways that your business can take advantage of it.